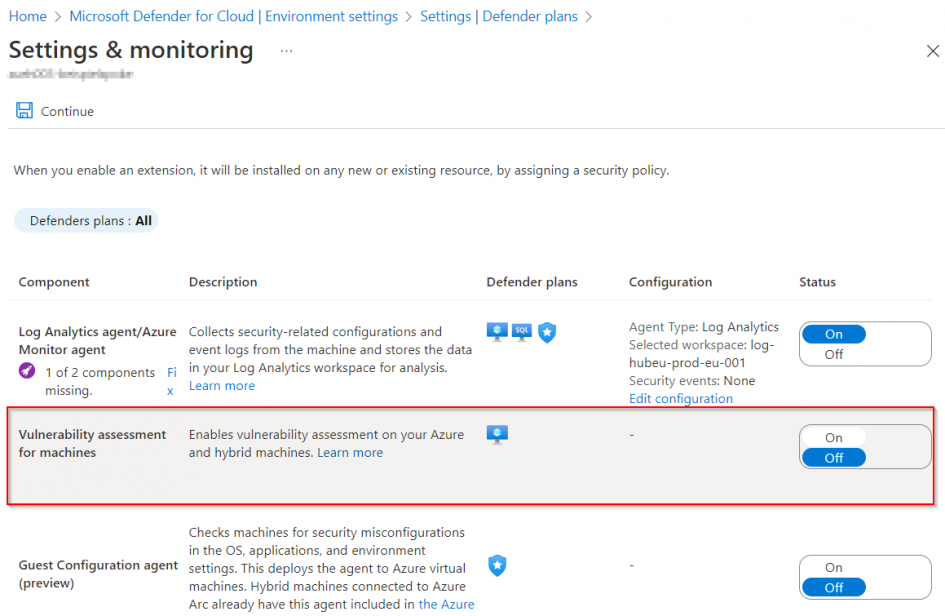
The Defender for Cloud offers are used to receive notifications and alerts about Azure Services. To do this, it can be activated per subscription and per Azure Service (e.g. with Set-AzSecurityPricing or in the portal). However, what is not supported by PowerShell and not listed in the API documentation is enabling the vulnerability assessment.
In order to enable the configuration via REST, the body and the URL can be read out in the portal when called. The URL: https://management.azure.com/subscriptions/$SubscriptionId/providers/Microsoft.Security/serverVulnerabilityAssessmentsSettings/AzureServersSetting?api-version=2022-01-01-preview must be called via PUT und must contain the following body (PowerShell notaion):
$body = @{
"kind" = "AzureServersSetting"
"properties" = @{
"selectedProvider" = "MdeTvm"
}
}
The Invoke-RestMethod can perform the PUT operation. It needs an access token of the current user and the content type must be specified to json:
$url = "https://management.azure.com/subscriptions/<SUBSCRIPTIONID>/providers/Microsoft.Security/serverVulnerabilityAssessmentsSettings/AzureServersSetting?api-version=2022-01-01-preview" Invoke-RestMethod ` -Method Put ` -ContentType "application/json; charset=utf-8" ` -Authentication Bearer ` -Token (ConvertTo-SecureString -String (Get-AzAccessToken).token -AsPlainText) ` -Body (ConvertTo-Json $body -Depth 2) ` -Uri $url
If the vulnerability assessment should be deactivated, the same PowerShell code and the same body can be used, only the method must be changed to delete.
Schreibe einen Kommentar