Kategorie Ops
If existing environments are recreated in Terraform, the resources already exist. Therefore, the resources must be transferred to the Statefile for management by Terraform. The output for a Terraform apply is: already exists – to be managed via Terraform this… Weiterlesen →
If the software and inventory functionality is only used for the supported regions, the new approach can be used via the AMA and the documentation can be followed, which unfortunately contains some errors. From August, the new way via AMA… Weiterlesen →
In order to use the software inventory and change tracking, regardless of the region, the deprecated Microsoft Monitoring Agent must currently be used. The solution uses an Azure Automation account that is connected to the MMA/OMS Extension and reports the… Weiterlesen →
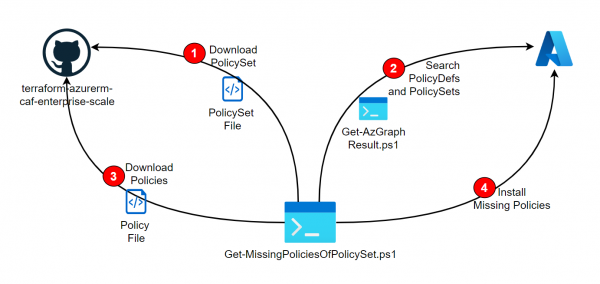
As described in the Post Deploy PolicySets from Azure Landing Zone Repository, PolicySets (Initiatives) can be installed directly from the Azure Landing Zone Repositiory. However, if these references other policies, they must already be installed beforehand. The following script is… Weiterlesen →
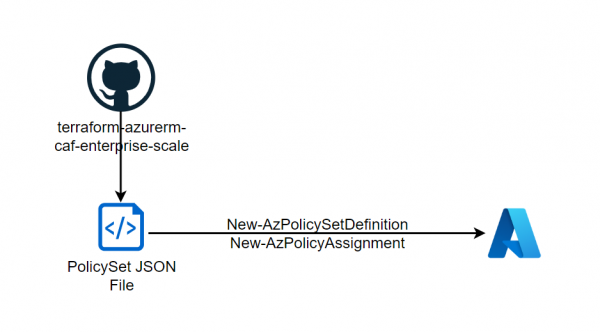
As described in the previous post, policies can be downloaded from the Enterprise Scale Architecture Repository and deployed into your own tenant. In addition to the mentioned policies, the repo also provides interesting Policy Initiatives (Policy Sets) that can also… Weiterlesen →
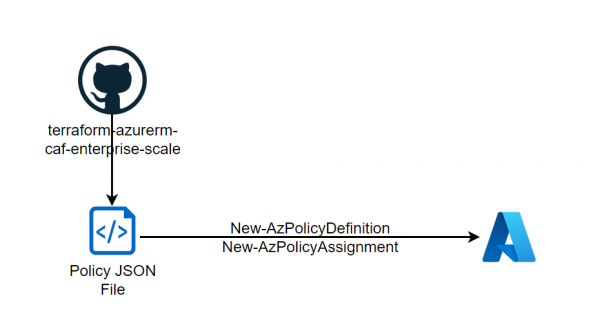
With the Enterprise Scale Architecture, Microsoft offers various landing zone designs that can be used directly as Terraform or Bicep. Interesting is that the repository also contains policies that are not available in the Azure portal. Microsoft recommends these policies… Weiterlesen →
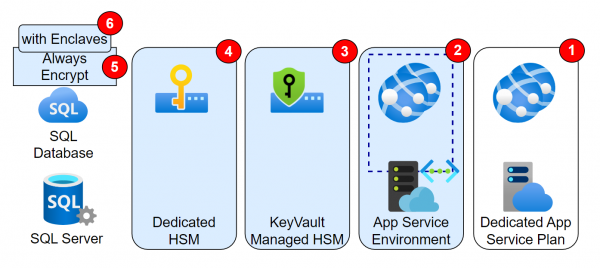
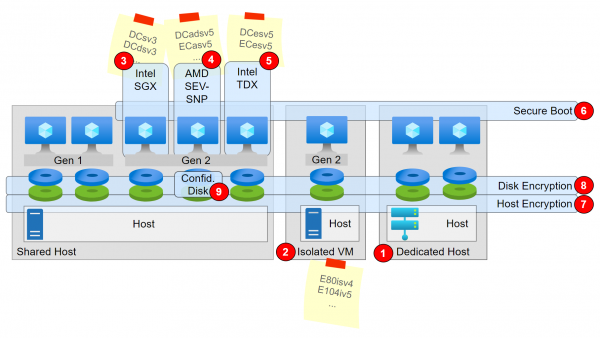
Introduction The previous article described the Confidential Computing features related to VMs. The same approach, i.e. securing data during processing, also applies to PaaS. These features will be discussed in this post. Features Featured not in the Picture
Introduction Microsoft refers to the CCC in its definition: The Confidential Computing Consortium defines confidential computing as: The protection of data in use by performing computations in a hardware-based Trusted Execution Environment (TEE). And describes the encryption of data-in-use in… Weiterlesen →
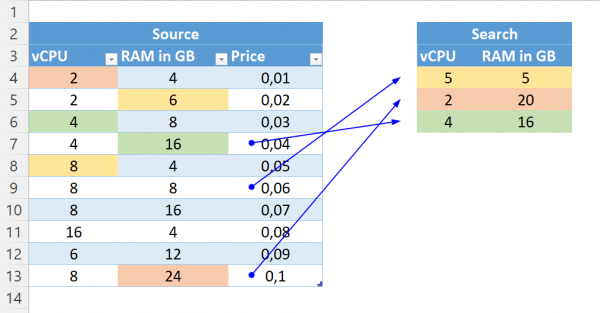
The Problem For OnPrem VMs, with specific vCPU and RAM, the right VM sizes often have to be found in Azure. It is important that the prices are as low as possible. For example, with Windows, a machine with 8… Weiterlesen →
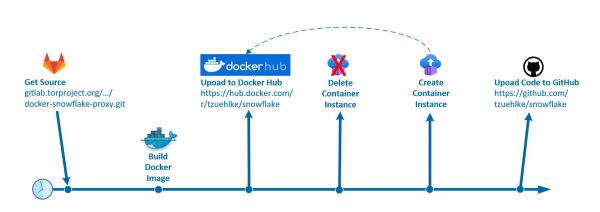
What is snowflake? „Snowflake is a system that allows people from all over the world to access censored websites and applications. Similar to how VPNs assist users in getting around Internet censorship, Snowflake helps you avoid being noticed by Internet… Weiterlesen →
Most resources in Azure can be well protected by disabling public access. If public access is completely deactivated, access can take place via private endpoints. In most cases it is sufficient to restrict access to selected network to use service… Weiterlesen →
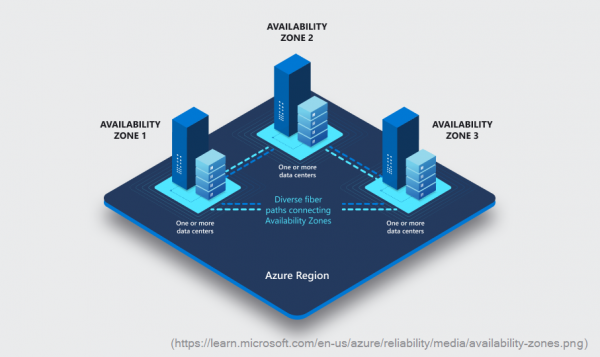
The concept of Availability Zones is well explained in the Microsoft documentation. These are different physical locations within a region that have separate power, cooling, and network infrastructure. When building a resource, it can often be decided in which Availability… Weiterlesen →
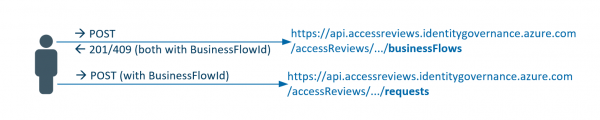
Azure resources (e.g. subscriptions) can be better protected with PIM. As a result, access roles are not granted permanently, but must be requested for a specified period of time. After this period, the permission is automatically revoked. If the PIM… Weiterlesen →
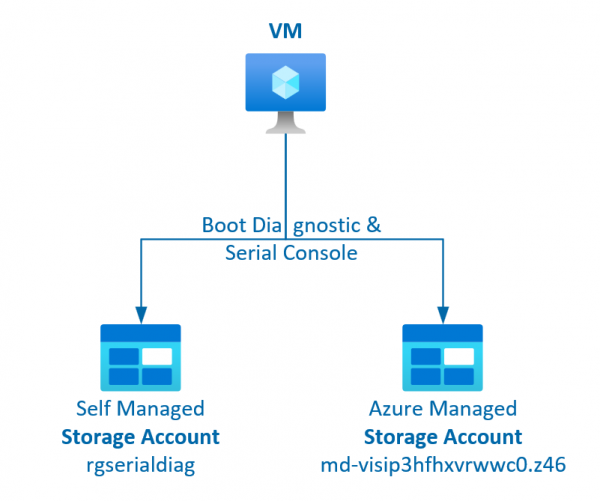
The serial console for VMs is a very useful tool for adapting the VM or making checks via the portal. For this, however, the boot diagnostics must be activated (i.e. a storage account for the logs must exist) and the… Weiterlesen →
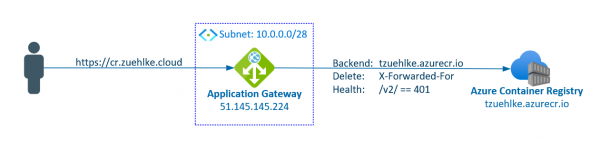
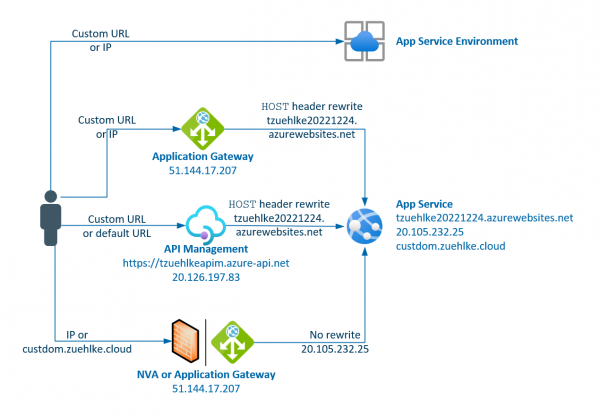
If an AppService is called directly via its IP, either the certificate is invalid or the page cannot be found. If the call is made via HTTPS, the automatic generated certificate only stores the DNS name and not the IP,… Weiterlesen →
Storage accounts are also often used as backend pools for Application Gateway. This allows the storage to be protected with private endpoints or service endpoints and accessed via a central entry point with an alternative URL. However, the Application Gateway… Weiterlesen →
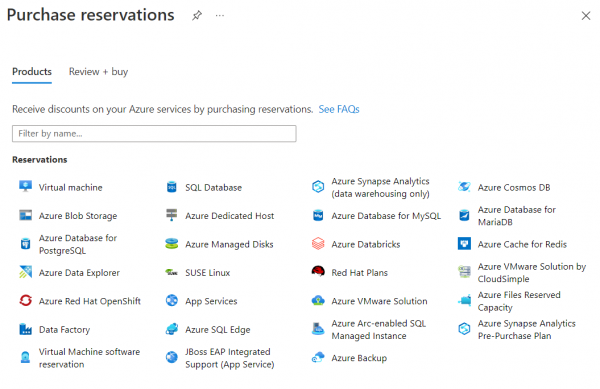
Various resources can be reserved in Azure, whereby use is guaranteed for 1 or 3 years. This can reduce the price of these resources by up to 72%. In the portal you can see these reduced costs for the reservations:… Weiterlesen →
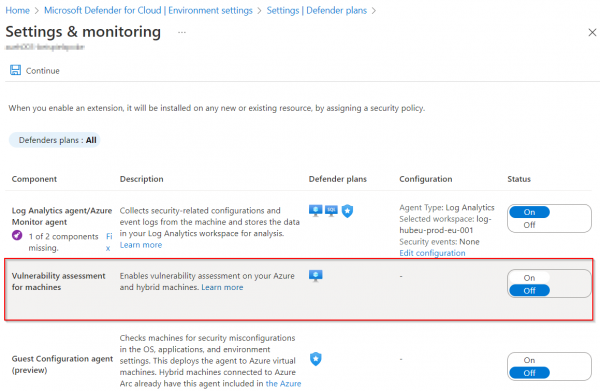
The Defender for Cloud offers are used to receive notifications and alerts about Azure Services. To do this, it can be activated per subscription and per Azure Service (e.g. with Set-AzSecurityPricing or in the portal). However, what is not supported… Weiterlesen →
To set up a budget with warning in Azure, the Az.Billing PowerShell Module offers the cmdlets New-AzConsumptionBudget. Unfortunately, the PowerShell commands don’t seem to be implemented correctly in version 2.0.0 at the Az Module 8.3.0 or newer (currently 9.0.1): The… Weiterlesen →
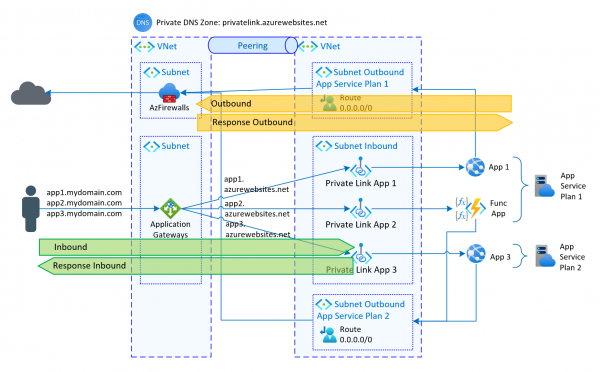
As described in the previous article, private endpoints can be used to securely access Azure services. With App Services there is an additional possibility to control the outgoing traffic. Specifically, when configuring the app service in the network area, 2… Weiterlesen →
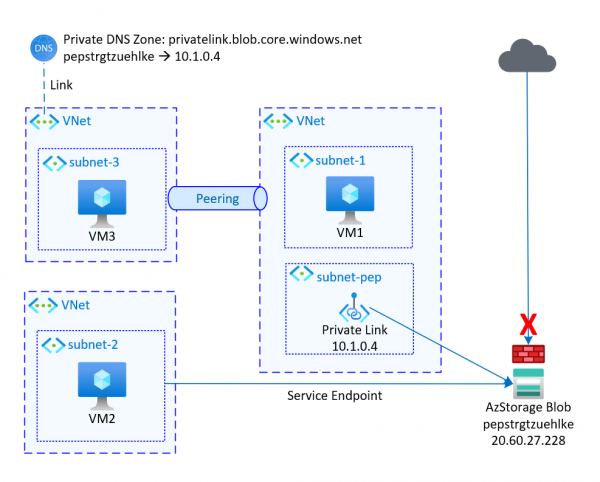
Most Azure services are accessible via a public URL. However, to provide a higher level of protection and a direct connection, various options are available in Azure. The two most common approaches are Service Endpoints and Private Endpoint/Private Link. Service… Weiterlesen →
„Blazor lets you build interactive web UIs using C# instead of JavaScript. Blazor apps are composed of reusable web UI components implemented using C#, HTML, and CSS.“ The application can be run directly in the browser as a WebAssembly. It… Weiterlesen →
I had problems with the instructions from my post, because Lets Encrypt is switching from ACME API v1 to ACME API v2. So I switched to acme.sh to generate Let’s Encrypt certificates in manual DNS mode. The steps are simple… Weiterlesen →
Keycloak is a comprehensive and free open source identity provider. It is also offered in numerous Docker variants, which makes deployment very easy. Access to the shell is necessary for the configuration, e.g. if the first user has to be… Weiterlesen →
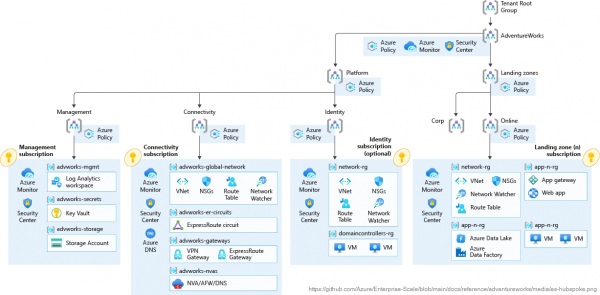
Lately people have been talking about Azure Landing Zones. This primarily refers to the environment in Azure into the workloads be migrated or new workloads are introduced. This means the preparation of the Azure environment. Specifically, the basic structure in… Weiterlesen →
VMs are often used in Azure because sometimes higher-quality services such as Platform Services are not suitable. For each VM, there is basic monitoring such as network traffic and corresponding visualizations (e.g. under Metrics) directly in the portal. Often, the… Weiterlesen →
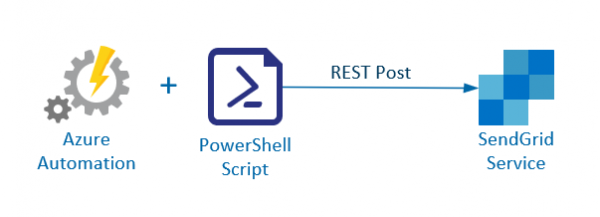
Azure Automation can automatically send emails through alerts when a runbook fails. Unfortunately, these alert mails cannot be adjusted and it is often necessary to send further information. In this case SendGrid is a good alternative because the mail service… Weiterlesen →
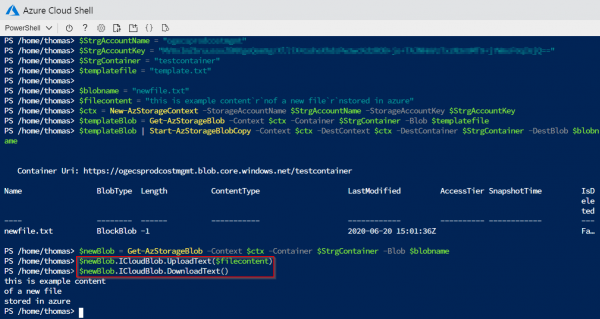
Should files are uploaded or downloaded from an Azure Storage Account Blob, there are corresponding PowerShell commands. Specifically, Get-AzStorageBlobContent or Set-AzStorageBlobContent can be used. Both commands always require the specification of a local file. In some cases, however, it may… Weiterlesen →
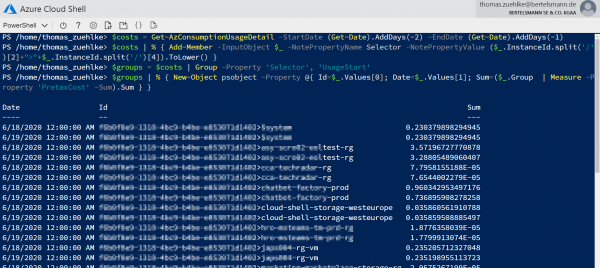
Azure provides a good way with Cost Management to report the costs and consumption of Azure Services. It offers various filtering, aggregation and export options. In some cases, however, it is still necessary to call up and process the data… Weiterlesen →
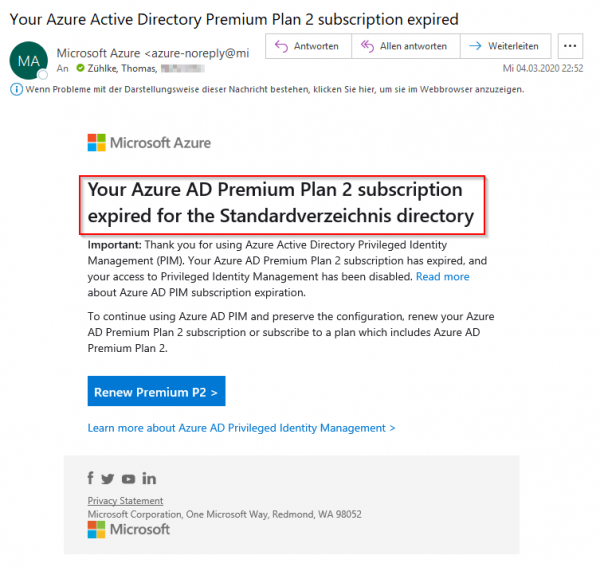
Anyone who has activated the Premium Plan 2 role of Azure Active Directory, for example for using Privilaged Identity Management (PIM), starts with a free 30-day trial period. If period has expired, the emails shown above follow daily and there… Weiterlesen →