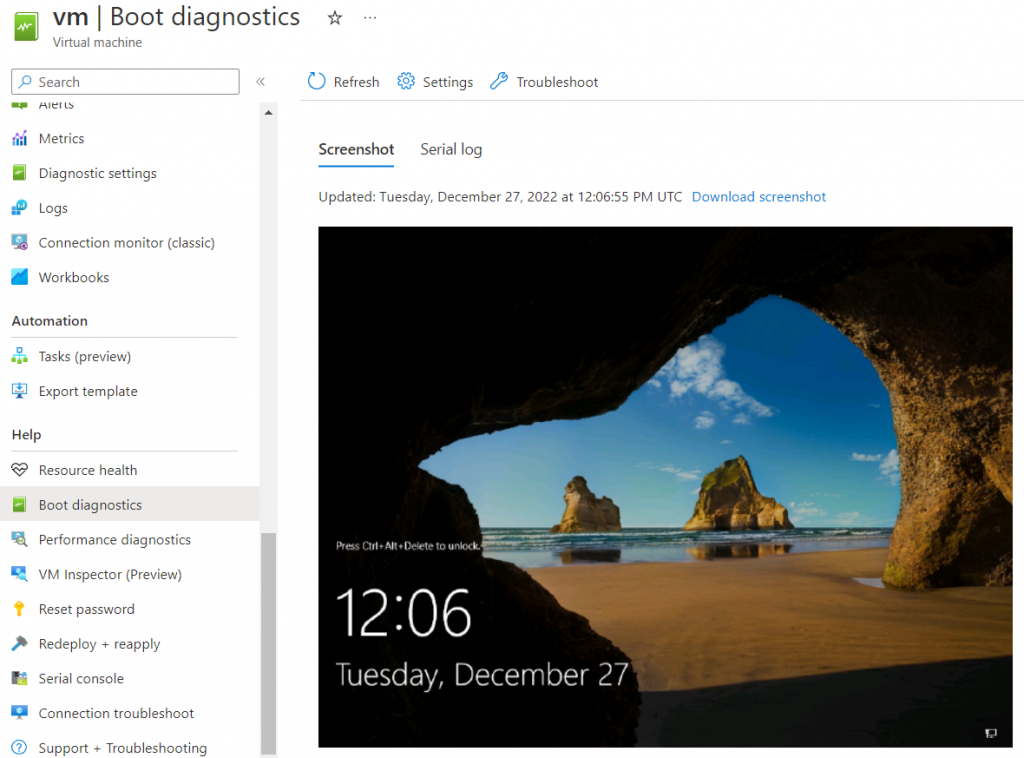
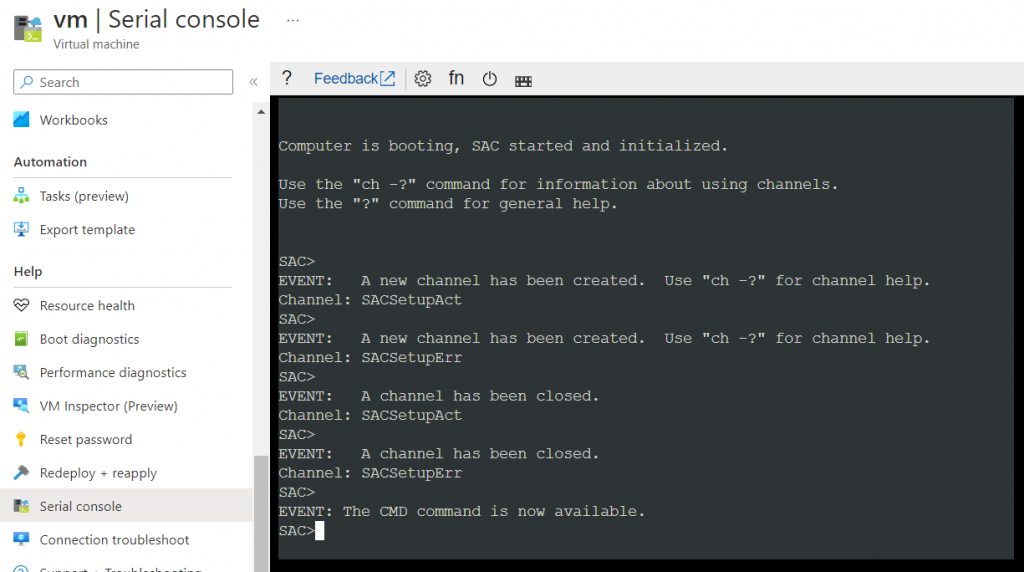
The serial console for VMs is a very useful tool for adapting the VM or making checks via the portal. For this, however, the boot diagnostics must be activated (i.e. a storage account for the logs must exist) and the serial console needs the appropriate access to it. If everything is configured correctly, both the boot diagnostics and the serial console can be used in the portal:
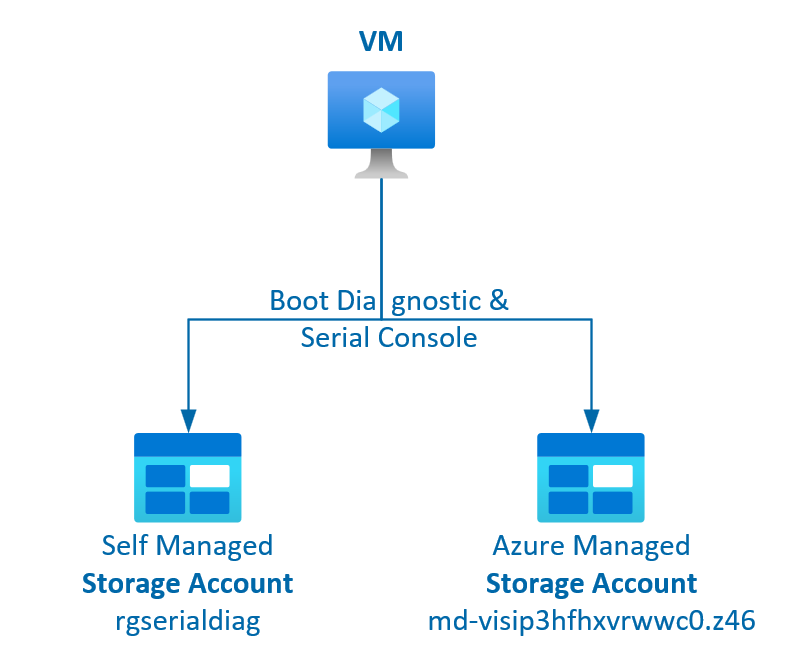
Self Managed Storage Account
If a separate storage account is used and it is secured, the configurations from the table are required. This also makes Boot Diagnostics and Serial Console work again. A look at the error FAQ often helps.
Storage Account Public network access | Steps for Boot Diagnostic (BD) and Serial Console (SC) |
|---|---|
is Enabled from all networks | BD & SC:✔️ No steps needed. |
is Enabled from selected virtual networks and IP addresses | BD:✔️Add Client IP to Storage Account Firewall exception SC: ✔️Add IPs from documentation to Storage Account Firewall |
is Disabled | BD & SC: ❌ Private Endpoints won’t work, even if you reconnect the storage account or try to use the privatelink URL: az vm boot-diagnostics enable --name <VM> --resource-group <RG> --storage https://<STRG>.blob.core.windows.netOnly solution is to use Enable with managed storage account instead. |
Azure Managed Storage Account
For some time there has been the option of using a storage account managed by Azure. Activation in the portal is sufficient for this:
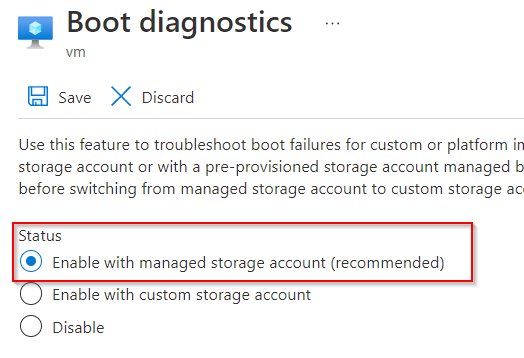
A storage account is created that is not listed in the portal. But the URL with SAS token can be retrieved:
az vm boot-diagnostics get-boot-log-uris -g rg-serial -n vm
{
"consoleScreenshotBlobUri": "https://md-visip3hfhxvrwwc0.z46.blob.storage.azure.net:443/0dd27e4d-c86e-4bdd-8a52-5539692f9d74/vm.e8b84998-dedb-493e-98ba-d3a64e5a15de.screenshot.bmp?sv=2018-03-28&...",
"serialConsoleLogBlobUri": "https://md-visip3hfhxvrwwc0.z46.blob.storage.azure.net:443/0dd27e4d-c86e-4bdd-8a52-5539692f9d74/vm.e8b84998-dedb-493e-98ba-d3a64e5a15de.serialconsole.log?sv=2018-03-28&..."
}
With this managed storage account, boot diagnostics and serial console work without any configuration and public access is automatically prevented.
Schreibe einen Kommentar