Kategorie Azure
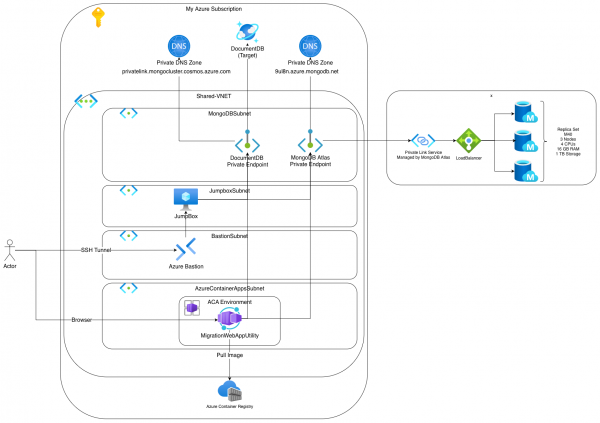
I am delighted to share this guest contribution on Thomas’ blog. As a former colleague and fellow Azure enthusiast, I’m excited to dive into MongoDB migration approaches and contribute to the conversation here. During my recent engagement I was tasked… Weiterlesen →
There are many different factors that come into play when planning the sequence of multiple migrations to the cloud. Regardless of whether it is different applications or a platform with different tenants, a sequence must be designed in each case…. Weiterlesen →
There are various ways to check the compliance status of Azure policies. It is common to check directly in the portal. However, automated processes are often implemented, such as queries with PowerShell or forwarding to Azure EventGrid. The most elegant… Weiterlesen →
A few weeks ago I was able to write a blog post about our App2Cloud approach. It explains how we at adesso support our customers with cloud adaptation. The approach also describes the prerequisites and steps for migrating and modernizing… Weiterlesen →
As shown in the previous post, it is easy to deploy a VM with bicep and Microsoft.Compute/virtualMachines. If it is an Azure Linux image, then the root user cannot be used for security reasons and access for SSH via username/password… Weiterlesen →
To deploy a VM with Bicep, the resource Microsoft.Compute/virtualMachines can be used. If the image from SQL Server is used, a Microsoft SQL Server is installed accordingly. However, a sample database or firewall rule is often required. These steps can… Weiterlesen →
If existing environments are recreated in Terraform, the resources already exist. Therefore, the resources must be transferred to the Statefile for management by Terraform. The output for a Terraform apply is: already exists – to be managed via Terraform this… Weiterlesen →
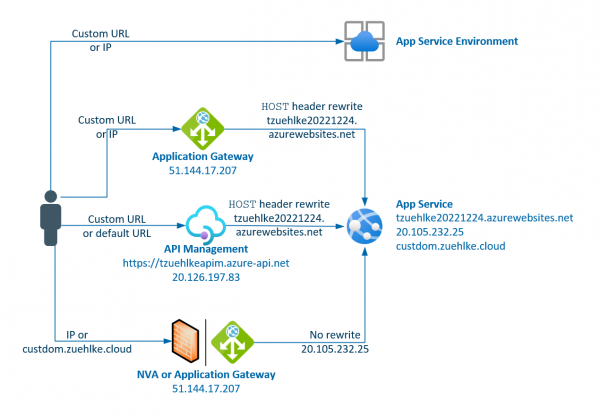
The Azure Application Gateway supports various routing options. With path-based routing, one or the other backend can be called depending on the URL. Things get a little more complicated when the apps on the app services are distributed in virtual… Weiterlesen →
The European Cloud Summit took place in Wiesbaden from May 14th to 16th. 3,000 participants and over 200 speakers met in the RheinMain CongressCenter. The sessions at the Cloud Summit were structured into 5 different tracks: Business and Strategy, Open… Weiterlesen →
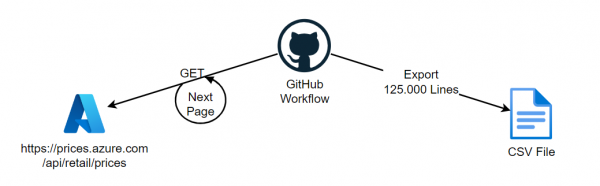
Idea A repository will be created in which the price history of Azure can be tracked. Since the API for pay-as-you-go prices does not provide historical data, a repository with past prices should be created as CSV files. These files… Weiterlesen →
If the software and inventory functionality is only used for the supported regions, the new approach can be used via the AMA and the documentation can be followed, which unfortunately contains some errors. From August, the new way via AMA… Weiterlesen →
In order to use the software inventory and change tracking, regardless of the region, the deprecated Microsoft Monitoring Agent must currently be used. The solution uses an Azure Automation account that is connected to the MMA/OMS Extension and reports the… Weiterlesen →
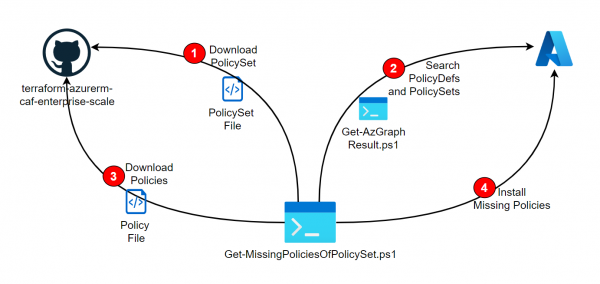
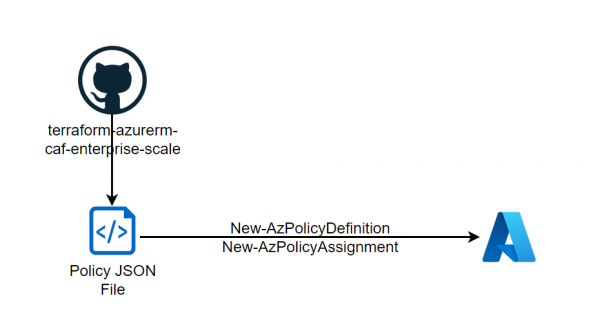
As described in the Post Deploy PolicySets from Azure Landing Zone Repository, PolicySets (Initiatives) can be installed directly from the Azure Landing Zone Repositiory. However, if these references other policies, they must already be installed beforehand. The following script is… Weiterlesen →
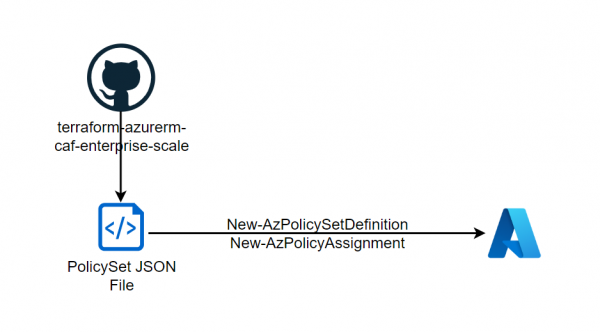
As described in the previous post, policies can be downloaded from the Enterprise Scale Architecture Repository and deployed into your own tenant. In addition to the mentioned policies, the repo also provides interesting Policy Initiatives (Policy Sets) that can also… Weiterlesen →
With the Enterprise Scale Architecture, Microsoft offers various landing zone designs that can be used directly as Terraform or Bicep. Interesting is that the repository also contains policies that are not available in the Azure portal. Microsoft recommends these policies… Weiterlesen →
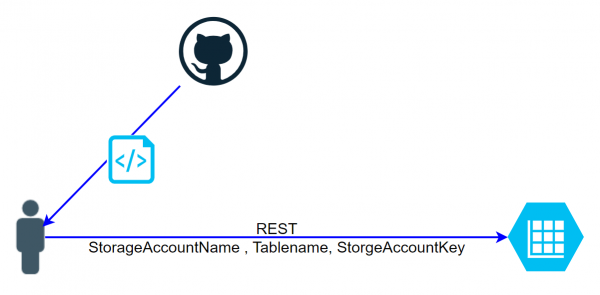
There are various ways to access a table of a storage account. If the storage account key is used, the request for the REST call must be generated in a complicated manner. The script getaztablerows.sh on Github shows the calculation:… Weiterlesen →
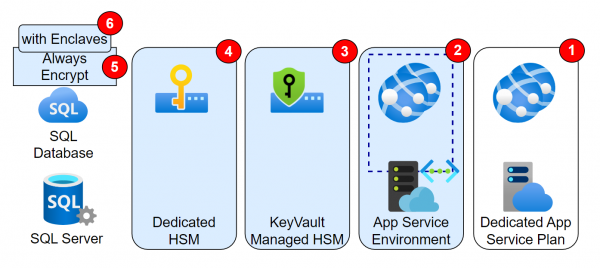
Introduction The previous article described the Confidential Computing features related to VMs. The same approach, i.e. securing data during processing, also applies to PaaS. These features will be discussed in this post. Features Featured not in the Picture
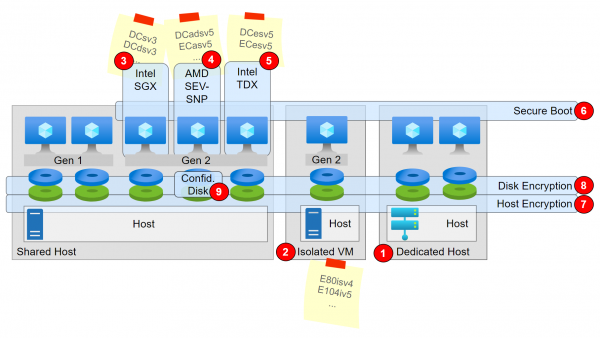
Introduction Microsoft refers to the CCC in its definition: The Confidential Computing Consortium defines confidential computing as: The protection of data in use by performing computations in a hardware-based Trusted Execution Environment (TEE). And describes the encryption of data-in-use in… Weiterlesen →
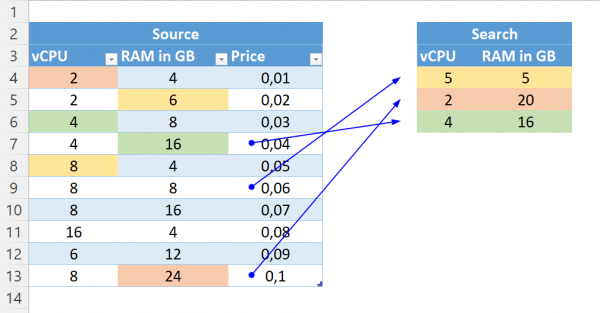
The Problem For OnPrem VMs, with specific vCPU and RAM, the right VM sizes often have to be found in Azure. It is important that the prices are as low as possible. For example, with Windows, a machine with 8… Weiterlesen →
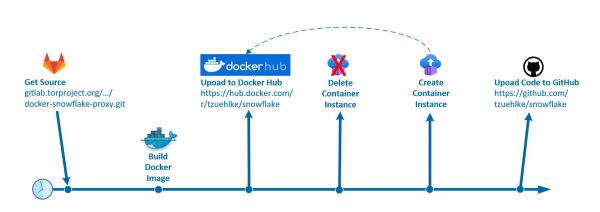
What is snowflake? „Snowflake is a system that allows people from all over the world to access censored websites and applications. Similar to how VPNs assist users in getting around Internet censorship, Snowflake helps you avoid being noticed by Internet… Weiterlesen →
Cloud governance plays a very important role in the adaptation of the cloud. Cloud governance defines the guidelines for the cloud, i.e. the restrictions that should apply in the cloud, but also the freedom that every user can have. The… Weiterlesen →
Bei der Adaption der Cloud spielt die Cloud Governance eine ganz wesentliche Rolle. Die Cloud Governance definiert die Richtlinien für die Cloud, also die Einschränkungen, die in der Cloud gelten sollen, aber auch die Freiheiten, die jeder User haben kann…. Weiterlesen →
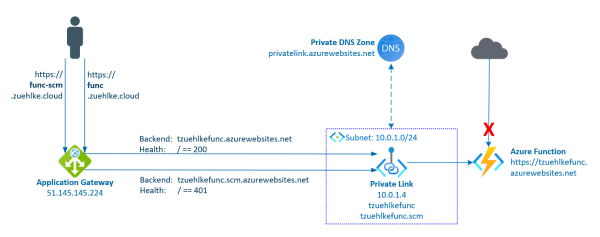
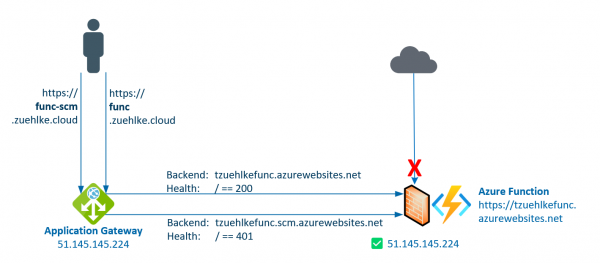
The previous post described how to deploy to an Azure Function if access is protected by an Application Gateway. Access to the function and to the management endpoint as well were protected. The Function was protected by the Function App… Weiterlesen →
Azure Functions are a serverless way to run code. They support different programming languages and can scale quickly. As a developer, it is particularly easy to deploy functions directly from Visual Studio or Visual Studio Code. Functions are often protected… Weiterlesen →
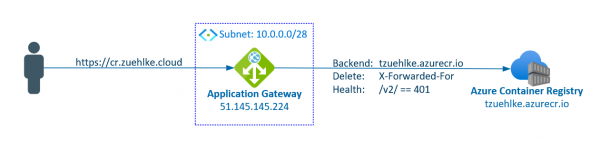
Most resources in Azure can be well protected by disabling public access. If public access is completely deactivated, access can take place via private endpoints. In most cases it is sufficient to restrict access to selected network to use service… Weiterlesen →
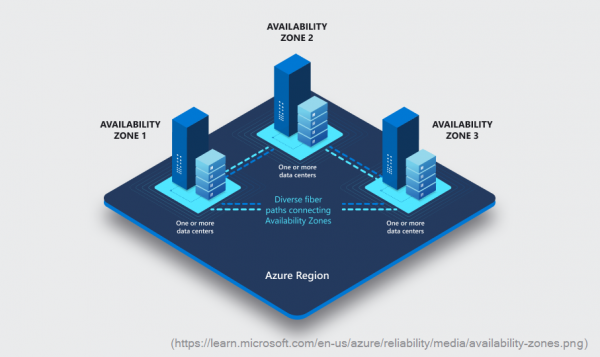
The concept of Availability Zones is well explained in the Microsoft documentation. These are different physical locations within a region that have separate power, cooling, and network infrastructure. When building a resource, it can often be decided in which Availability… Weiterlesen →
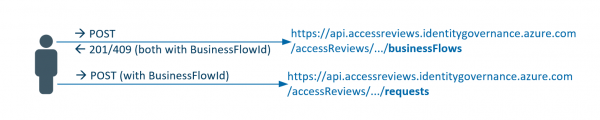
Azure resources (e.g. subscriptions) can be better protected with PIM. As a result, access roles are not granted permanently, but must be requested for a specified period of time. After this period, the permission is automatically revoked. If the PIM… Weiterlesen →
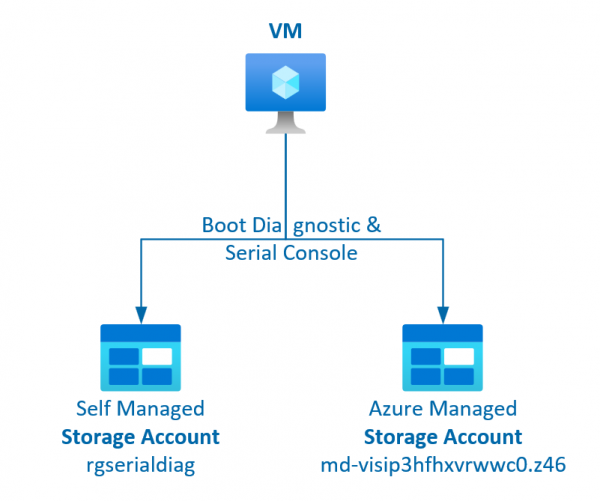
The serial console for VMs is a very useful tool for adapting the VM or making checks via the portal. For this, however, the boot diagnostics must be activated (i.e. a storage account for the logs must exist) and the… Weiterlesen →
If an AppService is called directly via its IP, either the certificate is invalid or the page cannot be found. If the call is made via HTTPS, the automatic generated certificate only stores the DNS name and not the IP,… Weiterlesen →
Storage accounts are also often used as backend pools for Application Gateway. This allows the storage to be protected with private endpoints or service endpoints and accessed via a central entry point with an alternative URL. However, the Application Gateway… Weiterlesen →